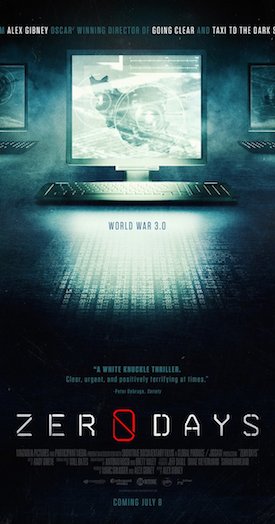
 Acclaimed filmmaker Alex Gibney’s Zero Days is a documentary thriller about the world of cyber war. For the first time, the film tells the complete story of Stuxnet, a piece of self-replicating computer malware (known as a “worm” for its ability to burrow from computer to computer on its own) that the U.S. and Israel unleashed to destroy a key part of an Iranian nuclear facility, and which ultimately spread beyond its intended target. Zero Days is the most comprehensive accounting to date of how a clandestine mission hatched by two allies with clashing agendas opened forever the Pandora’s Box of cyber warfare. Beyond the technical aspects of the story, Zero Days reveals a web of intrigue involving the CIA, the U.S. Military’s cyber command, Israel’s Mossad, and operations that include both espionage and covert assassinations but also a new generation of cyber weapons whose destructive power is matched only by Nuclear War. I sat down with Alex Gibney and Eric Chien, one of the digital security experts featured in the film who discovered Stuxnet.
Acclaimed filmmaker Alex Gibney’s Zero Days is a documentary thriller about the world of cyber war. For the first time, the film tells the complete story of Stuxnet, a piece of self-replicating computer malware (known as a “worm” for its ability to burrow from computer to computer on its own) that the U.S. and Israel unleashed to destroy a key part of an Iranian nuclear facility, and which ultimately spread beyond its intended target. Zero Days is the most comprehensive accounting to date of how a clandestine mission hatched by two allies with clashing agendas opened forever the Pandora’s Box of cyber warfare. Beyond the technical aspects of the story, Zero Days reveals a web of intrigue involving the CIA, the U.S. Military’s cyber command, Israel’s Mossad, and operations that include both espionage and covert assassinations but also a new generation of cyber weapons whose destructive power is matched only by Nuclear War. I sat down with Alex Gibney and Eric Chien, one of the digital security experts featured in the film who discovered Stuxnet.
Danny Miller: Alex, I spoke to you when your great doc We Steal Secrets: The Story of WikiLeaks came out a few years ago and wondered if that film was in some ways the parent of this film.
 Alex Gibney: Yeah, I guess you could say that. Working on the WikiLeaks story is what got me interested in this territory. And both films share a producer, Marc Shmuger, who was the one who reached out to me for both films.
Alex Gibney: Yeah, I guess you could say that. Working on the WikiLeaks story is what got me interested in this territory. And both films share a producer, Marc Shmuger, who was the one who reached out to me for both films.
I think one of the miracles of this film is that it makes the very complex subject matter intelligible to laypeople. I thought one of the most effective ways you did that was the balloon experiment where you show how Stuxnet could make a pump pop a balloon remotely.
Yeah, that was awesome.
Did you create that for the film or was it something that was already out there?
Eric Chien: What happened was in 2010 we were going to present at one of the biggest security conferences about Stuxnet and our discovery. Whenever I present at a conference, I like to have some kind of demo that shows people what we’re talking about. So we were thinking, “Well, we can’t really build a gigantic centrifuge like the ones in nuclear facilities —
Unless you wanted to expose every person in the room to radiation poisoning!
Right. (Laughs.) So we kept thinking about how we could show this code in action. First we thought we could maybe create something spinning or we could blow something up and finally we got the idea of getting a pump and using the code to make the pump go out of control by blowing a balloon up until it explodes.
So brilliant, because in that one second, we all get it. And then our minds immediately go to the endless possibilities of how that technology could be used to wreak endless havoc on our lives. I kept wondering why we haven’t had way more horrible incidents because of this.
Well, the truth is that a lot of things have happened. One example from last December, I don’t know if you remember this, but the power was completely cut off in Ukraine as a result of a cyber-attack. The power grid on the whole western half of the country was out for six hours. This is no longer science fiction, it’s not even “Oh, when’s the next thing going to happen?” Things are happening.
Alex Gibney: And one of the reasons the power came back so quickly during that episode is because Ukraine’s power grid is so old school. They literally still have levers and on-off switches.
Oh, so they were actually helped by the fact that their infrastructure is so antiquated?
Eric Chien: Yes. They basically just took their computers offline and went back to manual controls.
Would you say there’s any way to completely protect ourselves from something like Stuxnet?
Look, if anyone ever comes to you and tries to sell you 100 percent security, you should run in the opposite direction — there’s really no such thing.
Yeah, not even in our private computers or phones.
Exactly. Not in your home Mac or in the giant infrastructure of an entire nation, that kind of foolproof security just doesn’t exist.
Alex Gibney: Unless you’re using paper and pencil.
Eric Chien: Right. The reality is that it’s a constant cat and mouse game that we’re playing. Our best hope is that we are always staying one step ahead. But there’s no question that more bad things will happen. And then people ask us, “But why haven’t there been more huge disasters?” It’s not just about the technical capabilities because those are already there. What’s keeping worse things from happening more often is more about geopolitics than technology. But if the U.S. gets involved in some major skirmish and another country is willing to engage in this kind of cyber warfare and suffer the repercussions, it could happen.
And what almost scares me more is how some of these things seem to happen accidentally. Codes that can go out of control so even the people who invented them have no ability to stop the computer worms from spreading.
Stuxnet is the perfect example of that — it’s still out there right now spreading to people’s machines. And it will never stop, we’ll always see it spreading even though it’s unlikely that it will ever destroy another centrifuge plant. That was one of the many jaw-dropping moments for us when we realized that there are people who are willing to make the conscious decision to unleash such things knowing the enormous collateral damage that can result.
Do you think the people who created these codes fully realized the damage that could be done beyond their target?
Alex Gibney: Yes, I do. They just didn’t care.
But some of the reasons for creating Stuxnet, for example, having the ability to stop a nuclear attack from Iran, seemed sound. Would you agree with that and say that it just got out of control?
It was certainly a very ingenious device, and particularly ingenious because at first the malware was sending messages back to the engineers that all was well. The problem with these things, and I would include drones, is 1) What are the unintended consequences once you introduce this technology into the world, and 2) Once it spreads, you’ve now created a precedent that becomes the new norm and sends the message that you can do whatever you can get away with.
Yeah, it made me think about drones, too. And that psychological component that exists when you’re more physically involved in creating destruction — like when human beings have to fly over areas to bomb them versus having everything seem like a big video game.
That was one of the things that bothered the people in the NSA who came forward — they felt that the military folks in command didn’t properly appreciate the destructive capabilities of these cyber weapons. That they were used to thinking about nuclear weapons, conventional bombs and artillery, and so forth, but they didn’t fully grasp that if you’re shutting down someone’s grid, you’re also shutting down hospitals, life support systems, dialysis machines, all sorts of things like that. And if you’re doing it in an area where, unlike Ukraine, they’re much more computer-oriented, these things may not come right back up — you’ve done something that you can’t really control.
Alex, you’ve made a lot of films that, shall we say, didn’t exactly thrill some very powerful organizations and institutions. Do you expect people in those groups to try to discredit this film in any way?
Perhaps. We’ve heard about some people in national intelligence who weren’t happy about some of the information in our film but they didn’t try to prevent any of our screenings so far. You do need to be careful when you’re dealing with classified information. You certainly don’t want to put anyone at risk. We vetted everything that’s in the film with those considerations. But part of the job of a filmmaker is to sometimes say that certain things are so important that there is a need-to-know for the American public.
The scene in the film where we see official after official refusing to comment on Stuxnet is very effective. But when you were interviewing them, were you surprised that they were so unwilling to talk about it?
Yes. Frankly, I did expect a little more because Stuxnet had already happened and there had been a good deal of literature about it including Eric’s research. So when you have an extremely important event that people already know about, you would think that our public officials could comment on it. But no, most wouldn’t.
Do you ever worry about any personal repercussions from pissing off these powerful organizations?
No, you just can’t live that way, it would completely debilitate you. We certainly took precautions, and I was pretty certain I was being listened to. During the making of this film, we used encrypted phone calls and emails and we transcribed all of our conversations with our sources on electric typewriters, we didn’t use computers, and then we destroyed the original recordings.
What’s your ultimate hope for the film other than having more people become aware of these events?
In terms of policy, I think the public really needs to know more about what’s going on than we currently do. It’s ridiculous how much information is over-classified. That has to stop because it’s vital that we have discussions about some of the things that are being done in our name, we’re just keeping too much secret. What happens is that the people who are keeping these secrets start to develop contempt for average citizens who they don’t think have any right to know what’s going on. And I think that kind of contempt is not a healthy thing.
Being in the middle of a presidential campaign and knowing what you do about this technology, does the result of the upcoming election worry you?
Oh, I think having a President Trump with his finger on the button should scare anyone!